Increase your value – reduce your risks
Fact-based resources, research and information for your IT policies, controls, regulatory and internal audits.
We found it beneficial to assess different IT centers in the company.
— ,
Insurance industry
Fact-based resources, research and information for your IT policies, controls, regulatory and internal audits.
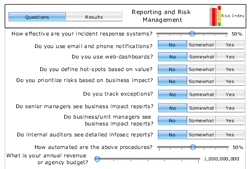
Find out the impact that your practices for reporting and risk management have on your outcomes and how they compare with your peers, industry and best performers.
What sets the leaders apart from 9-in-10 other firms when it comes to managing risk related to the uses of IT? Its’ not technology and it’s not complex mathematics in calculating risk scores. Instead, what sets the leaders apart from all others are a number of practices, including: – Senior business leaders who own the… more »
For some, managing IT has become a full-time job of managing vendor-delivered IT services. But for others, managing vendors that deliver information or IT resources is just a small part of what needs to be done. The early-stages of IT outsourcing – discrete in its focus and limited in extent – has evolved to include:… more »
Are you always being asked to do more with less resources, time and budgets for IT and information security? Learn from the best performers who always have more resources, time and budgets for IT and information security, and who consistently report and communicate on the business impacts of IT.
Is the use of Smartphones good for business? The answers are yes and no. Explore some of the compelling benefits, risks, and what the best-in-class are doing to manage both. And, find out why some are avoiding certain mobile devices and why.